Vercel Got Breached. Here's What You Need to Do Right Now.
Vercel confirmed unauthorized access to internal systems on April 19, 2026. ShinyHunters listed their data for $2M. Here's what to do right now if you're on Vercel.
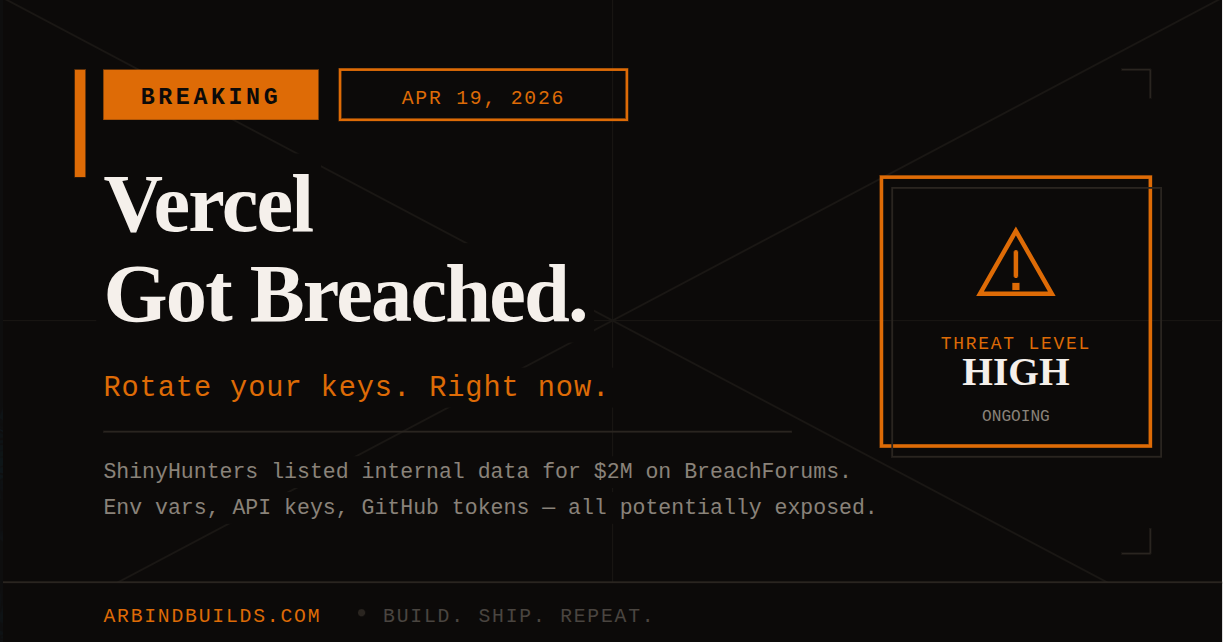
It happened today. Sunday morning, April 19, 2026, Vercel confirmed that someone got into their internal systems. If you have projects on Vercel, this matters to you.
What actually happened
Vercel published a security bulletin a few hours ago. Unauthorized access to internal systems, a limited number of customers directly affected, incident response team brought in, law enforcement notified. That's the official version.
The fuller picture: this came to light because someone claiming to be ShinyHunters posted on BreachForums offering to sell what they say is Vercel's internal data for $2 million. The listing claims it has source code, access keys, NPM tokens, GitHub tokens, employee accounts, and data from Vercel's internal Linear instance and user management systems.
Even if only part of that is real, it's a problem.
Rotate your keys. Now.
Vercel's official guidance is to review environment variables and use the sensitive environment variable feature. Theo (t3.gg) was more direct: env vars marked as "sensitive" in Vercel appear to be safe. Anything NOT marked sensitive should be rotated.
Go into your Vercel dashboard, open each project, and pull up environment variables. Anything that looks like a secret -- database URLs, API keys, third-party tokens -- rotate it at the source and update it in Vercel. While you're there, flip the "sensitive" toggle on every secret.
If you have GitHub connected to Vercel (most people do), check your connected GitHub token permissions too. Same for any NPM tokens.
A few things worth knowing
The full scope is still being worked out. Vercel says they're contacting impacted customers directly, so if you haven't heard from them, you might be fine -- but "might be fine" is not a reason to skip rotating keys.
Services are still running. This isn't a downtime situation, it's a credential exposure situation, which in some ways is worse. Nothing looks broken from the outside. That's the whole problem.
ShinyHunters is not some random anonymous post. They're a known threat actor group with real breaches behind them. That doesn't confirm the data is legit, but it's not a claim worth dismissing either.
Keep watching this
Vercel is updating their bulletin as the investigation moves forward:
https://vercel.com/kb/bulletin/vercel-april-2026-security-incident
What's confirmed right now: Vercel's internal systems were accessed without authorization. Everything else -- scope, what was actually taken, which customers are affected -- is still being investigated.
Rotate your keys. Mark them sensitive. Check that page again tonight.
Comments
Tagged